In Focus This Week
Election security updates
Physical security takes on an added urgency
By M. Mindy Moretti
electionline.org
Back in the pre-2020 halcyon days, the physical security of an election and the officials who conduct them, while important, took a bit of a backseat to concerns about cyberthreats.
The events surrounding and following the 2020 election changed all of that and state and local elections officials are now equally as focused on protecting the physical safety of themselves and poll workers as they are the cyber side of an election.
State Legislatures are passing bills, the Department of Justice is indicting offenders and groups from CISA to the U.S. Election Assistance Commission to the Committee for Safe and Secure Elections are providing tools to help state and local election officials stay safe.
Here’s a look at some of the work being done to secure elections workers in 2024 and beyond.
NEW! Physical Security Checklist From CISA
 This week, the Cybersecurity and Infrastructure Security Agency (CISA) released the Physical Security Checklist for Polling Locations, a new tool designed to bolster security preparedness for the frontline of U.S. elections.
This week, the Cybersecurity and Infrastructure Security Agency (CISA) released the Physical Security Checklist for Polling Locations, a new tool designed to bolster security preparedness for the frontline of U.S. elections.
The checklist, part of CISA’s suite of election security resources, is tailored to empower election workers with actionable and accessible security measures for locations serving as temporary election facilities.
“Protecting against physical threats to election locations like polling places where Americans cast their vote is one of the most significant responsibilities election officials bear. CISA is committed to doing anything we can to support this mission,” said CISA Senior Advisor Cait Conley. “The people who run elections and those who volunteer to work at polling places are heroes, and CISA is proud to support them, including with critical threat awareness and planning tools such as this checklist. While no measure can eliminate all risk, these resources empower officials to understand, mitigate, and address security challenges proactively.”
The resource is designed for simplicity, requiring no prior security expertise for implementation. It covers pre-planning and Election Day procedures and is adaptable to individual facility needs and resources. Through a series of yes or no questions, election workers and volunteers can assess potential security threats and incidents, aiding in the establishment and improvement of physical security measures.
The Physical Security Checklist for Polling Locations is one of a collection of resources CISA has developed to support the physical security of election infrastructure. The agency has Protective Security Advisors serving all 50 states, District of Columbia, and territories who support state and local election officials through sharing information, conducting physical security assessments of election facilities, and offering no-cost services and trainings on areas like de-escalation techniques, responding to active shooter situations, and other physical threat specific offerings to address the evolving threats facing election officials.
Legislation
 In its most recent update, dated April 12, The National Conference of State Legislatures reported that since 2020,18 states have enacted laws specifically addressing protections for election officials and poll workers. How states protect these individuals varies.
In its most recent update, dated April 12, The National Conference of State Legislatures reported that since 2020,18 states have enacted laws specifically addressing protections for election officials and poll workers. How states protect these individuals varies.
Ten states have criminalized intimidation and/or interference with election workers by establishing incarceration and fines for offenders.
Maine requires election workers to take classes in de-escalation tactics.
Arizona, California, Oregon and Washington allow election officials to be included in the state’s address confidentiality programs. Washington also specifically addresses cyber harassment.
Additionally, a number of states have recently passed legislation banning or limiting guns at polling places joining a growing list of states that already had some prohibition on the books
Prosecution
 In late March, the U.S. Department of Justice said that reports of widespread threats against officials running the 2020 and 2022 elections have resulted in charges against roughly 20 people, with more than a half dozen receiving sentences between one and 3½ years.
In late March, the U.S. Department of Justice said that reports of widespread threats against officials running the 2020 and 2022 elections have resulted in charges against roughly 20 people, with more than a half dozen receiving sentences between one and 3½ years.
However, at a press conference in Arizona, DOJ officials said that it remains to be seen if the stiff sentences will serve as an effective deterrent to would-be-criminals in future election cycles.
“Let these cases be a lesson not to take or attempt to take the rule of law into one’s own hands,” said U.S. Attorney Gary Restaino, Arizona’s top federal prosecutor.
Sentences in the cases pursued by the task force have ranged from 30 days to three and a half years, according to the Justice Department.
Even as officials touted their efforts at the press conference, DOJ official John Keller acknowledged that “the vast majority” of the disturbing and intimidating messages reported to the Justice Department can’t be prosecuted because they don’t appear to meet the Supreme Court’s standards for a so-called “true threat.”
Trainings
Several states made the news recently for the trainings they did (and continue to do) with officials from the Committee for Safe and Secure Elections.
 Michigan
Michigan
Recently, The Associated Press was granted access inside the committee’s training session in Traverse City and allowed to observe the scenarios election workers are likely to face this year and the discussions about how they and law enforcement can prepare for them.
At the Michigan training, former Rochester Hills Clerk Tina Barton and former Larimer County, Colorado Sheriff Justin Smith walked local officials through numerous scenarios they could encounter in the coming months.
“None of these scenarios are sensational. They are all things that have already happened in some way, shape or form across the country,” Barton told the group. “To say, ‘Oh, that could never happen.’ These things are already happening.”
According to the AP, Smith often speaks directly to the police officers and sheriff’s deputies in the room, explaining the role they play in elections and how the environment has changed since 2020. In past years, election officials were likely to deal with issues on their own, such as protesters or unruly citizens looking to promote their candidates at polling places.
“It’s not that simple anymore,” Smith tells the group. “We need to be at the table and be part of the solution.”
Michigan Secretary of State Jocelyn Benson, whose office helped sponsor and coordinate the Traverse City training, said it’s imperative for law enforcement and election officials to work together to ensure a smooth election in November.
Georgia
The Atlanta Journal-Constitution had an article this week on the trainings happening in the Peach State to prepare local election officials for November.
During a training exercise last week at Paulding County’s election office, sheriffs and election officials talked through how they would both ensure public safety and protect voting from interference.
“Hopefully it will not grow and get worse than it did in 2020, but I think there’s a chance it will,” said Chris Harvey, a former Georgia elections director who now oversees law enforcement training. “We’re not trying to make you really paranoid; we’re trying to make you a little paranoid and to plan for worst-case scenarios.”
Serious problems at polling places would require a police response. Election officials would need law enforcement if there were a bomb threat, voter intimidation or interference while election workers tried to count votes.
Minor situations could be managed by election officials, such as talking through a voter’s concerns in a quiet corner or by countering disinformation on social media platforms.
“Election threats are real, and we need to take them seriously,” Paulding County Elections Director Deidre Holden told the AJC. “November is going to be crazy. That’s usually when the most people come out, and you don’t want people to be agitated.”
electionline Daily News Email
 What’s the best part of waking up? electionline Daily News in your inbox of course so be sure to sign up for your daily dose.
What’s the best part of waking up? electionline Daily News in your inbox of course so be sure to sign up for your daily dose.
Each morning you’ll receive the top headlines of the day, plus a listing of states featured in that day’s news round up.
To sign up, simply visit our site and provide us with your email and you’ll begin receiving the news in your inbox each morning.
We Google so you don’t have to!
Election News This Week
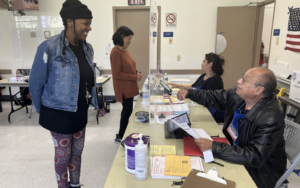
 2024 Primary Updates: Voters in the Commonwealth of Pennsylvania headed to the polls this week for their primary and by most reports, it was relatively smooth sailing on primary day. Secretary of the Commonwealth Al Schmidt reported that the election ran efficiently and successfully, noting minimal reports of routine issues from voters across Pennsylvania. “Dedicated and hard-working county election staff and poll workers across the Commonwealth have again conducted a free, fair, safe and secure election,” Schmidt said. “Voters, whether voting by mail or in person at their polling places, also deserve recognition for casting their ballots and ensuring their voices are heard.” Counties received nearly 896,000 mail ballot applications for the primary – more than 795,000 applications for no-excuse mail-in ballots and more than 100,000 applications for absentee ballots. As of the 8 p.m. return deadline, counties had received more than 75% of those completed ballots. “Very, very quiet” said Beth Hopkins, Lackawanna County Elections Director. “I would think that November will be much more busy.” Counties like Lancaster were considering Tuesday’s primary a test-run for November. Even counties, like Luzerne and Northampton, which have seen issues in the past, reported relatively few, if any problems. Issues did continue to plague Pennsylvania’s vote-by-mail process though. A design change Pennsylvania officials made to prevent voters from making a disqualifying error on their mail ballots seems to have tripped up a number of voters. Numerous counties reporting having to set aside improperly dated ballots. Tuesday proved to be a good day for the youth vote. At Lincoln High School in Mayfair nearly all of the poll workers were teenagers. Some Lincoln students. Others recent grads. “The kids know what they’re doing here, they get good reviews here. The adults who are here with them always give us very positive feedback. The community gives us positive feedback,” said Sarah Caswell, a special education and science teacher. The University of Pennsylvania serves as a polling site in Philadelphia and many students and staff serve as poll workers. Lucy Rupertus is a first-year political science major from Philadelphia who spent her inaugural primary day as a poll worker on Tuesday. Her voter-registration efforts inspired her to come out to work at the polls. “You spend all year getting people registered to vote and helping to put up signage on campus to encourage people to come out, and this is an opportunity to see the fruits of our labor,” she said. And on the opposite side of the state in the Pittsburgh area, exchange students from Georgia and Latvia got to see how American democracy works up close. “I’m learning about the importance of local government and the importance of voting and participating in local elections,” said Tengo Kandelaki, who met voters as they entered the polling site at Good Shepherd Lutheran Church in Hempfield’s West Point neighborhood.
2024 Primary Updates: Voters in the Commonwealth of Pennsylvania headed to the polls this week for their primary and by most reports, it was relatively smooth sailing on primary day. Secretary of the Commonwealth Al Schmidt reported that the election ran efficiently and successfully, noting minimal reports of routine issues from voters across Pennsylvania. “Dedicated and hard-working county election staff and poll workers across the Commonwealth have again conducted a free, fair, safe and secure election,” Schmidt said. “Voters, whether voting by mail or in person at their polling places, also deserve recognition for casting their ballots and ensuring their voices are heard.” Counties received nearly 896,000 mail ballot applications for the primary – more than 795,000 applications for no-excuse mail-in ballots and more than 100,000 applications for absentee ballots. As of the 8 p.m. return deadline, counties had received more than 75% of those completed ballots. “Very, very quiet” said Beth Hopkins, Lackawanna County Elections Director. “I would think that November will be much more busy.” Counties like Lancaster were considering Tuesday’s primary a test-run for November. Even counties, like Luzerne and Northampton, which have seen issues in the past, reported relatively few, if any problems. Issues did continue to plague Pennsylvania’s vote-by-mail process though. A design change Pennsylvania officials made to prevent voters from making a disqualifying error on their mail ballots seems to have tripped up a number of voters. Numerous counties reporting having to set aside improperly dated ballots. Tuesday proved to be a good day for the youth vote. At Lincoln High School in Mayfair nearly all of the poll workers were teenagers. Some Lincoln students. Others recent grads. “The kids know what they’re doing here, they get good reviews here. The adults who are here with them always give us very positive feedback. The community gives us positive feedback,” said Sarah Caswell, a special education and science teacher. The University of Pennsylvania serves as a polling site in Philadelphia and many students and staff serve as poll workers. Lucy Rupertus is a first-year political science major from Philadelphia who spent her inaugural primary day as a poll worker on Tuesday. Her voter-registration efforts inspired her to come out to work at the polls. “You spend all year getting people registered to vote and helping to put up signage on campus to encourage people to come out, and this is an opportunity to see the fruits of our labor,” she said. And on the opposite side of the state in the Pittsburgh area, exchange students from Georgia and Latvia got to see how American democracy works up close. “I’m learning about the importance of local government and the importance of voting and participating in local elections,” said Tengo Kandelaki, who met voters as they entered the polling site at Good Shepherd Lutheran Church in Hempfield’s West Point neighborhood.
 Ballot Verifier: In Ada County, Idaho a team of election experts are hard at work to combat doubts of election integrity. County Clerk Trent Tripple and the county elections team are set to launch a first-of-its-kind election data and transparency site. “This level of transparency and the access to this data is not happening anywhere else that I’m aware of,” Tripple said. The Ballot Verifier tool will host a record of every ballot, every box filled in, for every Ada County race moving forward. Easy to access data and scans of ballots for a legitimate full record of election results. However, the public can rest easy as the names on the ballots are removed. Ada County elections said the tool, “will allow the public to explore a wide range of Ada County election data, including ballot images and Cast Vote Records (CVR) for all elections from 2022 forward. The Ballot Verifier is designed to ensure the accuracy and integrity of every vote cast in Ada County elections. It allows voters to verify that ballots are being tabulated correctly, while also providing peace of mind that their voices were heard accurately.” Saul Seyler is the Elections Director for Ada County. He walked KTVB through the new tool which will launch this week, with complete data going back to 2022. “We want everyone to be able to trust in the election process. And this will provide some ultimate transparency into the ballots cast and how they were read,” Seyler said. The county is working with CIVERA, a company that looks to use technology to build a better democracy. “Ada County, Idaho, is the first to launch the surveyors ballot verifier,” Adam Friedman, CEO said. “This ushers in a new era of American democracy. Frankly, where the technology is there, the technology makes all of this possible. There’s really no more excuse for jurisdictions around the country to provide that window into these live operations and into, you know, into the deepest levels of our election process so that everyone feels like together, you know, we’re all seeing honest results. And we know that people who are being elected really belong there and are there to serve us.”
Ballot Verifier: In Ada County, Idaho a team of election experts are hard at work to combat doubts of election integrity. County Clerk Trent Tripple and the county elections team are set to launch a first-of-its-kind election data and transparency site. “This level of transparency and the access to this data is not happening anywhere else that I’m aware of,” Tripple said. The Ballot Verifier tool will host a record of every ballot, every box filled in, for every Ada County race moving forward. Easy to access data and scans of ballots for a legitimate full record of election results. However, the public can rest easy as the names on the ballots are removed. Ada County elections said the tool, “will allow the public to explore a wide range of Ada County election data, including ballot images and Cast Vote Records (CVR) for all elections from 2022 forward. The Ballot Verifier is designed to ensure the accuracy and integrity of every vote cast in Ada County elections. It allows voters to verify that ballots are being tabulated correctly, while also providing peace of mind that their voices were heard accurately.” Saul Seyler is the Elections Director for Ada County. He walked KTVB through the new tool which will launch this week, with complete data going back to 2022. “We want everyone to be able to trust in the election process. And this will provide some ultimate transparency into the ballots cast and how they were read,” Seyler said. The county is working with CIVERA, a company that looks to use technology to build a better democracy. “Ada County, Idaho, is the first to launch the surveyors ballot verifier,” Adam Friedman, CEO said. “This ushers in a new era of American democracy. Frankly, where the technology is there, the technology makes all of this possible. There’s really no more excuse for jurisdictions around the country to provide that window into these live operations and into, you know, into the deepest levels of our election process so that everyone feels like together, you know, we’re all seeing honest results. And we know that people who are being elected really belong there and are there to serve us.”
 This and That: The Arkansas State Board of Election Commissioners approved an emergency rule that bars election officials from accepting voter registration forms signed with an electronic signature. In Leon County, Florida, Supervisor of Elections Mark Earley announced that his office will pick up the tab for vote-by-mail postage, starting with the Aug. 20 primary. Following an investigation by the Iowa Capital Dispatch, the state’s Health and Human Services Department pledged to do better about registering clients to vote. With early voting underway for the May 14 primary, elections officials in Nebraska say that the rollout of voter ID in the first statewide election since it became law is going well. The USPS announced this week it will continue with its plan to reroute Reno-area mail processing to Sacramento, a move that drew bipartisan ire from Nevada lawmakers while raising questions about the rate at which mail ballots can be processed. Over the next few weeks, election officials in all 88 Ohio counties will be going through extra training to prepare. It’s called the ‘Ready for November’ initiative and it was started in 2020 by Secretary of State Frank LaRose. Votebeat has a story about the lengths and costs Brazos County, Texas is going to in an effort to appease concerned citizens about the integrity of the county’s elections. The Wisconsin Elections Commission’s effort to create a new rule to guide the conduct of election observers at polling places received a public hearing this week. Supporters and opponents expressed their opinions, which included the airing of false claims of election fraud that have hounded the agency for the past four years. Approximately 27% of Sheridan County, Wyoming voters were purged from the rolls, most for not voting in the 2022 general election.
This and That: The Arkansas State Board of Election Commissioners approved an emergency rule that bars election officials from accepting voter registration forms signed with an electronic signature. In Leon County, Florida, Supervisor of Elections Mark Earley announced that his office will pick up the tab for vote-by-mail postage, starting with the Aug. 20 primary. Following an investigation by the Iowa Capital Dispatch, the state’s Health and Human Services Department pledged to do better about registering clients to vote. With early voting underway for the May 14 primary, elections officials in Nebraska say that the rollout of voter ID in the first statewide election since it became law is going well. The USPS announced this week it will continue with its plan to reroute Reno-area mail processing to Sacramento, a move that drew bipartisan ire from Nevada lawmakers while raising questions about the rate at which mail ballots can be processed. Over the next few weeks, election officials in all 88 Ohio counties will be going through extra training to prepare. It’s called the ‘Ready for November’ initiative and it was started in 2020 by Secretary of State Frank LaRose. Votebeat has a story about the lengths and costs Brazos County, Texas is going to in an effort to appease concerned citizens about the integrity of the county’s elections. The Wisconsin Elections Commission’s effort to create a new rule to guide the conduct of election observers at polling places received a public hearing this week. Supporters and opponents expressed their opinions, which included the airing of false claims of election fraud that have hounded the agency for the past four years. Approximately 27% of Sheridan County, Wyoming voters were purged from the rolls, most for not voting in the 2022 general election.
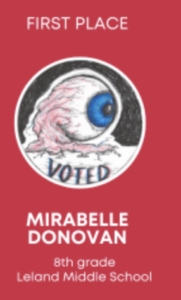
 Sticker News: The Brunswick County, North Carolina Board of Elections announced the winners of its highly anticipated inaugural “I Voted” and “Future Voter” Sticker Design Contest. The competition was open to all Brunswick County public, private, charter and home school students in grades K-12. Students were invited to showcase their creativity and the response was an array of vibrant and imaginative submissions. After careful deliberation by a panel of judges, which included the five members of the Brunswick County Board of Elections and five Board of Elections staff members, we are excited to unveil the winners. In the “I Voted” contest First Place was awarded toMirabelle Donovan, 8th grade, Leland Middle School In the “Future Voter” contest, First Place was awarded to : Celine Tendo, 8th grade, Shallotte Middle School. Winners will be presented with trophies, gift cards and copies of their sticker. The art teachers for the first-place winners will also receive a gift card. The first-place designs will be printed for the upcoming General Election this fall and voters can look forward to receiving their stickers when voting in the Presidential election. In addition, the Brunswick County Board of Elections plans to offer the competition in future presidential election years. “We were blown away by the level of creativity and innovation demonstrated by all the participants,” said Sara LaVere, Director at
Sticker News: The Brunswick County, North Carolina Board of Elections announced the winners of its highly anticipated inaugural “I Voted” and “Future Voter” Sticker Design Contest. The competition was open to all Brunswick County public, private, charter and home school students in grades K-12. Students were invited to showcase their creativity and the response was an array of vibrant and imaginative submissions. After careful deliberation by a panel of judges, which included the five members of the Brunswick County Board of Elections and five Board of Elections staff members, we are excited to unveil the winners. In the “I Voted” contest First Place was awarded toMirabelle Donovan, 8th grade, Leland Middle School In the “Future Voter” contest, First Place was awarded to : Celine Tendo, 8th grade, Shallotte Middle School. Winners will be presented with trophies, gift cards and copies of their sticker. The art teachers for the first-place winners will also receive a gift card. The first-place designs will be printed for the upcoming General Election this fall and voters can look forward to receiving their stickers when voting in the Presidential election. In addition, the Brunswick County Board of Elections plans to offer the competition in future presidential election years. “We were blown away by the level of creativity and innovation demonstrated by all the participants,” said Sara LaVere, Director at  the Brunswick County Board of Elections. “Each design was a testament to the incredible talent within our student community, and we are grateful to everyone who shared their artwork with us.” Julia Dicks, a senior at Loveland Classical Schools in Larimer County, Colorado is the winner of the 2024 “I Voted” sticker contest. Julia’s design was chosen from public voting. “Larimer County
the Brunswick County Board of Elections. “Each design was a testament to the incredible talent within our student community, and we are grateful to everyone who shared their artwork with us.” Julia Dicks, a senior at Loveland Classical Schools in Larimer County, Colorado is the winner of the 2024 “I Voted” sticker contest. Julia’s design was chosen from public voting. “Larimer County  residents cast their vote throughout the week of April 8-12 and I’m thrilled to announce Julia Dicks, a senior at Loveland Classical Schools as the winner of the “I Voted” sticker design contest,” Larimer County Clerk & Recorder Tina Harris said. In February, local area high school students were invited to participate in Larimer County’s first-ever “I Voted” sticker design contest. After an internal review of the submissions made, the top ten finalists were selected. When polls opened to the community on April 8th, residents were encouraged to cast their vote with the winning design to be featured on the stickers issued to all Larimer County voters in the November 2024 General Election. The Panola County, Texas Elections Office has announced Jadyn Baker as the 2024 I Voter Sticker Contest winner. “All of our students did an outstanding job on their designs
residents cast their vote throughout the week of April 8-12 and I’m thrilled to announce Julia Dicks, a senior at Loveland Classical Schools as the winner of the “I Voted” sticker design contest,” Larimer County Clerk & Recorder Tina Harris said. In February, local area high school students were invited to participate in Larimer County’s first-ever “I Voted” sticker design contest. After an internal review of the submissions made, the top ten finalists were selected. When polls opened to the community on April 8th, residents were encouraged to cast their vote with the winning design to be featured on the stickers issued to all Larimer County voters in the November 2024 General Election. The Panola County, Texas Elections Office has announced Jadyn Baker as the 2024 I Voter Sticker Contest winner. “All of our students did an outstanding job on their designs  and can’t wait to see what you all come up with next time!,” the office said. The second annual “I Voted” sticker contest let kids ages 10-18 design stickers to be given to voters during the November elections. Participants were asked to design a logo that will be used for 2-inch square stickers and digital graphics for the Nov. 5 general election. The Genesee County, New York Board of Elections announced the winners of its second “I Voted” sticker contest. The contest, coordinated by the Board of Elections, showcased the creative talent of local students and their involvement in the electoral process. The contest received many submissions, with over 300 outstanding entries from Genesee County schools. ‘It was a tough decision to select our seven finalists,’ said Lorie Longhany, Democratic Election Commissioner. ‘We can’t wait to see the students’ graphic designs in print and used in our outreach efforts! ’The winning designs will be featured on the “I Voted” stickers distributed to voters as they cast their ballots in November. They will also be utilized for voter outreach and promoted across social media platforms. The grand prize winner was Tyler Caldwell of Alexander.
and can’t wait to see what you all come up with next time!,” the office said. The second annual “I Voted” sticker contest let kids ages 10-18 design stickers to be given to voters during the November elections. Participants were asked to design a logo that will be used for 2-inch square stickers and digital graphics for the Nov. 5 general election. The Genesee County, New York Board of Elections announced the winners of its second “I Voted” sticker contest. The contest, coordinated by the Board of Elections, showcased the creative talent of local students and their involvement in the electoral process. The contest received many submissions, with over 300 outstanding entries from Genesee County schools. ‘It was a tough decision to select our seven finalists,’ said Lorie Longhany, Democratic Election Commissioner. ‘We can’t wait to see the students’ graphic designs in print and used in our outreach efforts! ’The winning designs will be featured on the “I Voted” stickers distributed to voters as they cast their ballots in November. They will also be utilized for voter outreach and promoted across social media platforms. The grand prize winner was Tyler Caldwell of Alexander.
 Congratulations: Congratulations to reporter Miles Parks and his team at NPR for being nominated for a Peabody Award. The Peabody Awards Board of Jurors today announced the 41 nominees for the Documentary, News, Public Service, and Radio/Podcast categories selected to represent the most compelling and empowering stories released in broadcasting and streaming media during 2023. The nominees were chosen by a unanimous vote of 32 jurors from over 1,100 entries from television, podcasts/radio and the web in entertainment, news, documentary, arts, children’s/youth, public service, and multimedia programming. Parks and the NPR team were nominated for their piece, “How the Far Right is Making Voting Fraud Easier” In a months-long reporting project, NPR uncovered the conservative movement working to sabotage the ERIC system, despite the Republican Party’s claims that it is dedicated to catching and rooting out voting improprieties.
Congratulations: Congratulations to reporter Miles Parks and his team at NPR for being nominated for a Peabody Award. The Peabody Awards Board of Jurors today announced the 41 nominees for the Documentary, News, Public Service, and Radio/Podcast categories selected to represent the most compelling and empowering stories released in broadcasting and streaming media during 2023. The nominees were chosen by a unanimous vote of 32 jurors from over 1,100 entries from television, podcasts/radio and the web in entertainment, news, documentary, arts, children’s/youth, public service, and multimedia programming. Parks and the NPR team were nominated for their piece, “How the Far Right is Making Voting Fraud Easier” In a months-long reporting project, NPR uncovered the conservative movement working to sabotage the ERIC system, despite the Republican Party’s claims that it is dedicated to catching and rooting out voting improprieties.
Personnel News: Bay County, Florida Supervisor of Elections Mark Anderson announced his retirement after more than 23 years on the job. Anoka County, Minnesota elections manager Tom Hunt, has been promoted to elections director. Washington County, Wisconsin Clerk Ashley Reichert announced that she will be seeking re-election as in the 2024 fall election. Abigail Goldman has been appointed acting director on a temporary basis of the Baltimore City board of elections.The move was necessitated by medical leave taken by longtime director Armstead Jones, said board president Scherod Barnes. Kenny Rhyne is the new director of elections for Burke County, North Carolina.
 In Memoriam: Tim Dowling retired chief deputy city commissioner, former supervisor of elections, longtime election finance and document specialist, and single dad, died Wednesday, April 17, of colon cancer. He was 61. A lifelong Philadelphian, Dowling served as chief deputy to city commissioner Lisa M. Deeley from 2016 until his retirement in 2022. Before that, he was supervisor of elections from 2012 to 2016 and election finance and document specialist from 1996 to 2012. He joined the city commissioners’ office as a temporary assistant in 1987, was mentored by former commissioner Marge Tartaglione in the 1980s and ‘90s, and became such an expert on election law and campaign finance that Deeley drafted him as her chief deputy when she assumed office in 2015. In an online tribute, Deeley said: “I surprised everyone by hiring Timmy, which instantly made me a player. … He taught me one call, one conversation, at a time.” In all, Mr. Dowling served in the city commissioners’ office for 35 years. He started as a ward leader in Northeast Philadelphia and soon became a regular at the city’s voter registration office. He told The Inquirer in 1996: “You can register as many people to vote as you want. But if they don’t come out to vote, it’s worthless.”
In Memoriam: Tim Dowling retired chief deputy city commissioner, former supervisor of elections, longtime election finance and document specialist, and single dad, died Wednesday, April 17, of colon cancer. He was 61. A lifelong Philadelphian, Dowling served as chief deputy to city commissioner Lisa M. Deeley from 2016 until his retirement in 2022. Before that, he was supervisor of elections from 2012 to 2016 and election finance and document specialist from 1996 to 2012. He joined the city commissioners’ office as a temporary assistant in 1987, was mentored by former commissioner Marge Tartaglione in the 1980s and ‘90s, and became such an expert on election law and campaign finance that Deeley drafted him as her chief deputy when she assumed office in 2015. In an online tribute, Deeley said: “I surprised everyone by hiring Timmy, which instantly made me a player. … He taught me one call, one conversation, at a time.” In all, Mr. Dowling served in the city commissioners’ office for 35 years. He started as a ward leader in Northeast Philadelphia and soon became a regular at the city’s voter registration office. He told The Inquirer in 1996: “You can register as many people to vote as you want. But if they don’t come out to vote, it’s worthless.”
New Research, Reports, Studies
 Poll Worker Motivation: A study by a University of Montana faculty member recently investigated the motivations of people who serve on the frontlines of democracy and found public service is a top reason poll workers sign up for the job. Money is a motivator, too. Published in the current issue of the Public Administration Quarterly, the study was conducted by UM faculty member Christina Barsky. “Election officials are raising the alarm: The problem of poll worker recruitment is more than a localized problem — it is a timely concern for democracy,” said the study. In an interview with the Daily Montanan, Barsky said she started working with the Missoula County Elections Office in 2015 and became interested in the public servants who give their time to make democracy work — for low or no pay. “I think one of the really incredible things about our democratic process in Montana and in the United States is the process is run by our friends and neighbors,” Barsky said. The study, based on data from more than 1,000 poll workers in four Arizona counties, found public service, or “duty as a citizen” and being “the kind of person who contributes my share,” as a top motivator. Some 91% rated “duty as a citizen” as an important factor in serving as a poll worker — 62% as very important and 29% as somewhat important. Some 93% rated being “the kind of person who contributes my share” as important — 59% as very important and 34% as somewhat important. But social engagement is also a motivator, according to survey results. The survey found 68% rated “I found it exciting” as an important factor, and 72% rated “I like to meet new people” as an important factor. Barksy said the results show the elections space provides a necessary connection to community, especially for seniors. “If you’re not going to work day in and day out, or if you’re not going to a religious service, it’s providing that social connection that I think particularly individuals that are retired look for,” Barsky said. Poll workers also want to earn extra money, according to the results. Some 51% rated compensation as an important factor — 22% as very important and 29% as somewhat important.
Poll Worker Motivation: A study by a University of Montana faculty member recently investigated the motivations of people who serve on the frontlines of democracy and found public service is a top reason poll workers sign up for the job. Money is a motivator, too. Published in the current issue of the Public Administration Quarterly, the study was conducted by UM faculty member Christina Barsky. “Election officials are raising the alarm: The problem of poll worker recruitment is more than a localized problem — it is a timely concern for democracy,” said the study. In an interview with the Daily Montanan, Barsky said she started working with the Missoula County Elections Office in 2015 and became interested in the public servants who give their time to make democracy work — for low or no pay. “I think one of the really incredible things about our democratic process in Montana and in the United States is the process is run by our friends and neighbors,” Barsky said. The study, based on data from more than 1,000 poll workers in four Arizona counties, found public service, or “duty as a citizen” and being “the kind of person who contributes my share,” as a top motivator. Some 91% rated “duty as a citizen” as an important factor in serving as a poll worker — 62% as very important and 29% as somewhat important. Some 93% rated being “the kind of person who contributes my share” as important — 59% as very important and 34% as somewhat important. But social engagement is also a motivator, according to survey results. The survey found 68% rated “I found it exciting” as an important factor, and 72% rated “I like to meet new people” as an important factor. Barksy said the results show the elections space provides a necessary connection to community, especially for seniors. “If you’re not going to work day in and day out, or if you’re not going to a religious service, it’s providing that social connection that I think particularly individuals that are retired look for,” Barsky said. Poll workers also want to earn extra money, according to the results. Some 51% rated compensation as an important factor — 22% as very important and 29% as somewhat important.
Election Cybersecurity Updates
Poll Vaulting
Cyber Threats to Global Elections
Today, Google Cloud’s Mandiant released its global elections report, offering a comprehensive look at the cyber threats Mandiant has historically observed in this  domain.
domain.
”We are facing a multitude of election cyberthreats. Several actors are emboldened and interested in interfering in the democratic process. Cyber espionage, information operations, and hacktivism will all be in play to some degree,” said John Hultquist, Mandiant Chief Analyst, Google Cloud
Actors who have previously targeted elections, like those tied to Russian military intelligence and Iran’s Islamic Revolutionary Guard Corps remain the boldest and most aggressive actors that Mandiant tracks. While they are constantly adapting their techniques, many of their operations follow a familiar formula: attacks with limited practical effects are exaggerated for maximum psychological impact.
“We will have to strike a balance between preparing for these threats while also being careful not to exaggerate their impacts,” Hulquist said. “This isn’t 2016. Though there are more actors in play, many are struggling to build and maintain influence in an environment where their operations are regularly identified and removed.”
Key points from the report include:
- The election cybersecurity landscape globally is characterized by a diversity of targets, tactics, and threats. Elections attract threat activity from a variety of threat actors including: state-sponsored actors, cyber criminals, hacktivists, insiders, and information operations as-a-service entities. Mandiant assesses with high confidence that state-sponsored actors pose the most serious cybersecurity risk to elections;
- Operations targeting election-related infrastructure can combine cyber intrusion activity, disruptive and destructive capabilities, and information operations, which include elements of public-facing advertisement and amplification of threat activity claims. Successful targeting does not automatically translate to high impact. Many threat actors have struggled to influence or achieve significant effects, despite their best efforts;
- The attack surface of an election involves a wide variety of entities beyond voting machines and voter registries. In fact, our observations of past cycles indicate that cyber operations target the major players involved in campaigning, political parties, news and social media more frequently than actual election infrastructure;
- Securing elections requires a comprehensive understanding of many types of threats and tactics, from distributed denial of service (DDoS) to data theft to deepfakes, that are likely to impact elections in 2024. It is vital to understand the variety of relevant threat vectors and how they relate, and to ensure mitigation strategies are in place to address the full scope of potential activity;
- Election organizations should consider steps to harden infrastructure against common attacks, and utilize account security tools to protect high-risk accounts;
- It’s important to note that wary and experienced defenders and populations are harder targets and without the element of surprise, adversaries are at a disadvantage.
The cybersecurity community must keep pace as more than two billion voters worldwide are expected to head to the polls in 2024. With elections in more than an estimated 50 countries, there is an opportunity to dynamically track how threats to democracy evolve. Understanding how threats are targeting one country will enable us to better anticipate and prepare for upcoming elections globally. At the same time, we must also appreciate the unique context of different countries. Election threats to South Africa, India, and the United States will inevitably differ in some regard. In either case, there is an opportunity for us to prepare with the advantage of intelligence.
Legislative Updates
 Alabama: The Senate Judiciary Committee, in a 4-4-3 vote, refused to let the bill, HB100, out of committee after two Republicans expressed concerns over punishing angry voters with a “crime of moral turpitude” if they are convicted of an assault for a relatively minor offense such as pointing their finger in a poll worker’s chest. The committee’s chairman, Sen. Will Barfoot, R-Pike Road, said the legislation, despite the defeat, will get “carried over” and placed on the Senate agenda to “give members time to look at it.” Barfoot voted in favor of moving the bill to the full Senate for consideration. Under HB100, increased penalties would apply against someone who commits a crime against an election official if that crime is motivated by the officials’ role in working at the polls during an election day. If a felony is committed against the election official, which is motivated by an individual’s role as an election official, then they would be disqualified from voting. The felony would be considered a crime of “moral turpitude.” In Alabama, those crimes include some of the most serious offenses of murder, rape, kidnapping, sexual abuse and torture, human trafficking, terrorism, child sex abuse, etc. It was voted out of the Alabama House with a 95-0 vote on April 16.
Alabama: The Senate Judiciary Committee, in a 4-4-3 vote, refused to let the bill, HB100, out of committee after two Republicans expressed concerns over punishing angry voters with a “crime of moral turpitude” if they are convicted of an assault for a relatively minor offense such as pointing their finger in a poll worker’s chest. The committee’s chairman, Sen. Will Barfoot, R-Pike Road, said the legislation, despite the defeat, will get “carried over” and placed on the Senate agenda to “give members time to look at it.” Barfoot voted in favor of moving the bill to the full Senate for consideration. Under HB100, increased penalties would apply against someone who commits a crime against an election official if that crime is motivated by the officials’ role in working at the polls during an election day. If a felony is committed against the election official, which is motivated by an individual’s role as an election official, then they would be disqualified from voting. The felony would be considered a crime of “moral turpitude.” In Alabama, those crimes include some of the most serious offenses of murder, rape, kidnapping, sexual abuse and torture, human trafficking, terrorism, child sex abuse, etc. It was voted out of the Alabama House with a 95-0 vote on April 16.
 Mississippi: Thirty-two Mississippians convicted of felonies could get their voting rights back after lawmakers advanced suffrage bills April 22, weeks after a Senate leader killed a broader bill that would have restored suffrage to many more people with criminal records. The move is necessary due to Mississippi’s piecemeal approach to restoring voting rights to people convicted of felony offenses who have paid their debts to society. To have voting rights restored, people convicted of any of the crimes must get a pardon from the governor or persuade lawmakers to pass individual bills just for them, with two-thirds approval of the House and Senate. Lawmakers in recent years have passed few of those bills, and they passed none in 2023. “I certainly don’t think this is the best way to do it,” said Republican Rep. Kevin Horan of Grenada, who chairs the House Judiciary B Committee. “There comes a point in time where individuals who have paid their debt to society, they’re paying taxes, they’re doing the things they need to do, there’s no reason those individuals shouldn’t have the right to vote.” Despite lawmakers’ dismay with the current process, some are trying to restore suffrage for select individuals. On Monday, lawmakers on House and Senate Judiciary committees passed a combined 32 bills. The bills were introduced after a House hearing on April 17 highlighted the difficulties some former felons face in regaining the right to vote. In March, the Republican-controlled Mississippi House passed a bill that would have allowed automatic restoration of voting rights for anyone convicted of theft, obtaining money or goods under false pretense, forgery, bigamy or “any crime interpreted as disenfranchising in later Attorney General opinions.” But the bill died after Senate Constitution Committee Chairwoman Angela Hill, a Republican from Picayune, refused to bring it up. Horan said the Republican House majority would only bring up individual suffrage bills for those who committed nonviolent offenses and had been discharged from custody for at least five years. Democratic Rep. Zakiya Summers of Jackson said she appreciated the House and Senate committees for passing the individual bills, but decried the death of the larger House bill.
Mississippi: Thirty-two Mississippians convicted of felonies could get their voting rights back after lawmakers advanced suffrage bills April 22, weeks after a Senate leader killed a broader bill that would have restored suffrage to many more people with criminal records. The move is necessary due to Mississippi’s piecemeal approach to restoring voting rights to people convicted of felony offenses who have paid their debts to society. To have voting rights restored, people convicted of any of the crimes must get a pardon from the governor or persuade lawmakers to pass individual bills just for them, with two-thirds approval of the House and Senate. Lawmakers in recent years have passed few of those bills, and they passed none in 2023. “I certainly don’t think this is the best way to do it,” said Republican Rep. Kevin Horan of Grenada, who chairs the House Judiciary B Committee. “There comes a point in time where individuals who have paid their debt to society, they’re paying taxes, they’re doing the things they need to do, there’s no reason those individuals shouldn’t have the right to vote.” Despite lawmakers’ dismay with the current process, some are trying to restore suffrage for select individuals. On Monday, lawmakers on House and Senate Judiciary committees passed a combined 32 bills. The bills were introduced after a House hearing on April 17 highlighted the difficulties some former felons face in regaining the right to vote. In March, the Republican-controlled Mississippi House passed a bill that would have allowed automatic restoration of voting rights for anyone convicted of theft, obtaining money or goods under false pretense, forgery, bigamy or “any crime interpreted as disenfranchising in later Attorney General opinions.” But the bill died after Senate Constitution Committee Chairwoman Angela Hill, a Republican from Picayune, refused to bring it up. Horan said the Republican House majority would only bring up individual suffrage bills for those who committed nonviolent offenses and had been discharged from custody for at least five years. Democratic Rep. Zakiya Summers of Jackson said she appreciated the House and Senate committees for passing the individual bills, but decried the death of the larger House bill.
 Minnesota: The Senate approved an elections policy bill April 18 that would guarantee voters the right to sue if they face vote suppression or vote dilution. On a 35-32 vote, the DFL-led chamber approved the provision as part of a broader bill with one Republican, Sen. Carla Nelson of Rochester, siding with them One item in the bill, which backers are calling the “Minnesota Voting Rights Act,” would guarantee in state law protections previously afforded under the 1965 federal Voting Rights Act. The 8th Circuit of the U.S. Court of Appeals last year ruled against a provision of the law that allowed voters to challenge voting policies or maps that were racially discriminatory. The court said that since voters weren’t directly named in the law, the right to challenge doesn’t apply. Senate President Bobby Joe Champion, DFL-Minneapolis, said Minnesota should cement the policy in state law and let voters sue over voter suppression and vote dilution, which is a racially driven form of preventing minority communities from electing candidates due to political boundaries being drawn in a fashion that prevents it. The broader elections bill would also use a person’s address prior to incarceration for setting voting maps, rather than counting their residence in the region where they are incarcerated. It would also sharpen the teeth of a state law that makes it a crime to make and share distorted images and videos intended to influence an election — often called deep fakes. The bill returns to the House to have changes confirmed before moving to the desk of DFL Gov. Tim Walz.
Minnesota: The Senate approved an elections policy bill April 18 that would guarantee voters the right to sue if they face vote suppression or vote dilution. On a 35-32 vote, the DFL-led chamber approved the provision as part of a broader bill with one Republican, Sen. Carla Nelson of Rochester, siding with them One item in the bill, which backers are calling the “Minnesota Voting Rights Act,” would guarantee in state law protections previously afforded under the 1965 federal Voting Rights Act. The 8th Circuit of the U.S. Court of Appeals last year ruled against a provision of the law that allowed voters to challenge voting policies or maps that were racially discriminatory. The court said that since voters weren’t directly named in the law, the right to challenge doesn’t apply. Senate President Bobby Joe Champion, DFL-Minneapolis, said Minnesota should cement the policy in state law and let voters sue over voter suppression and vote dilution, which is a racially driven form of preventing minority communities from electing candidates due to political boundaries being drawn in a fashion that prevents it. The broader elections bill would also use a person’s address prior to incarceration for setting voting maps, rather than counting their residence in the region where they are incarcerated. It would also sharpen the teeth of a state law that makes it a crime to make and share distorted images and videos intended to influence an election — often called deep fakes. The bill returns to the House to have changes confirmed before moving to the desk of DFL Gov. Tim Walz.
 Ohio: A bill introduced earlier this month would further tighten the state’s voter ID rules, allow the hand-counting of ballots in certain cases and require voting machines and electronic pollbooks to meet strict cybersecurity rules. House Bill 472 deals with complex, behind-the-scenes procedures for administering elections. Rep. Bernie Willis, R-Springfield, said the measure aims to revise outdated standards and ensure Ohio has a plan should it fall victim to cyberattacks before an election. The bill’s prospects are uncertain. Secretary of State Frank LaRose said it includes some good ideas, but other parts are entirely unworkable or need significant revision. A spokesman for House Speaker Jason Stephens, R-Kitts Hill, said he’s reviewing the bill, which will be assigned to a committee in the near future. Under House Bill 472: Ohioans would be required to provide a BMV-issued driver’s license or state ID to register to vote and vote by mail, unless they have a religious objection to being photographed. Voters can currently use their Social Security number; Counties would have to hand-count ballots if voters approve the procedure in a general election. To put the question on the ballot, a group must submit a petition signed by 2% of voters in the county; Voters who are flagged as non-citizens have 30 days to confirm their citizenship to election officials, or their registration would be canceled; Absentee ballots that aren’t properly sealed in envelopes wouldn’t be counted unless the voter appears at the board of elections to seal it; and The state auditor would annually audit the statewide voter registration database and three county registration systems.
Ohio: A bill introduced earlier this month would further tighten the state’s voter ID rules, allow the hand-counting of ballots in certain cases and require voting machines and electronic pollbooks to meet strict cybersecurity rules. House Bill 472 deals with complex, behind-the-scenes procedures for administering elections. Rep. Bernie Willis, R-Springfield, said the measure aims to revise outdated standards and ensure Ohio has a plan should it fall victim to cyberattacks before an election. The bill’s prospects are uncertain. Secretary of State Frank LaRose said it includes some good ideas, but other parts are entirely unworkable or need significant revision. A spokesman for House Speaker Jason Stephens, R-Kitts Hill, said he’s reviewing the bill, which will be assigned to a committee in the near future. Under House Bill 472: Ohioans would be required to provide a BMV-issued driver’s license or state ID to register to vote and vote by mail, unless they have a religious objection to being photographed. Voters can currently use their Social Security number; Counties would have to hand-count ballots if voters approve the procedure in a general election. To put the question on the ballot, a group must submit a petition signed by 2% of voters in the county; Voters who are flagged as non-citizens have 30 days to confirm their citizenship to election officials, or their registration would be canceled; Absentee ballots that aren’t properly sealed in envelopes wouldn’t be counted unless the voter appears at the board of elections to seal it; and The state auditor would annually audit the statewide voter registration database and three county registration systems.
Republican lawmakers have put out at least four different proposals to close Ohio’s partisan primaries since the start of the legislative session last year. The most recent to be introduced and heard, House Bill 437, would also prohibit candidates from running with a political party if that candidate had not voted in the party’s latest primary. HB 437 requires voters and candidates who are switching parties alike to declare their affiliation at least 90 days before an election. “Our belief is this will help deter those who intend to manipulate the results of our primaries,” Rep. Beth Lear (R-Galena) said in her committee testimony. “Each party should have the right to determine their own candidates for general election without meddling from the outside.” Right now, Ohio conducts partially open primaries—meaning voters in partisan elections don’t have to decide which side’s ballot they will cast until they submit their mail-in ballot application or arrive at the polls.
 Oklahoma: The Senate passed a bill that would impact how Oklahomans vote for their elected leaders. House Bill 3156 bans the state from offering ranked-choice voting, where voters can rank a list of candidates instead of choosing just one. The process would do away with runoffs, and some said it would allow for voters to not have to choose a candidate because they are the lesser of two evils. Republicans argued that the state shouldn’t change a system that already works fine and are concerned voters may think they have to list candidates on a preference list, even if they disagree with their positions. The bill passed off the Senate floor 37-8 along party lines. The bill is on its way to the governor, signifying a good chance Oklahoma won’t have ranked-choice voting anytime soon.
Oklahoma: The Senate passed a bill that would impact how Oklahomans vote for their elected leaders. House Bill 3156 bans the state from offering ranked-choice voting, where voters can rank a list of candidates instead of choosing just one. The process would do away with runoffs, and some said it would allow for voters to not have to choose a candidate because they are the lesser of two evils. Republicans argued that the state shouldn’t change a system that already works fine and are concerned voters may think they have to list candidates on a preference list, even if they disagree with their positions. The bill passed off the Senate floor 37-8 along party lines. The bill is on its way to the governor, signifying a good chance Oklahoma won’t have ranked-choice voting anytime soon.
Legal Updates
 U.S. Supreme Court: The U.S. Supreme Court declined to take up two separate elections-related cases this week. SCOTUS rejected an appeal brought by Arizona Republicans Kari Lake and Mark Finchem, bringing finality to the duo’s legal effort challenging the use of electronic voting machines two years to the day after it began. Lake, a candidate for U.S. Senate, and Finchem, a candidate for state Senate, asked the nation’s top court to hear their case in mid-March. The court declined to consider it, making that official with an order on Monday that does not include details of the court’s decision. Legal experts had predicted the court would not exercise its discretion to add the case to its docket, citing well-established legal precedent and the court’s low acceptance rate. The court also rejected a challenge to voting rules in Texas that automatically let senior citizens − but not younger people − vote by mail. Mail-in balloting has become a partisan debate as Democrats champion it as a way to increase turnout and Republicans argue it increases the risk of voter fraud. The court declined to hear an appeal brought by three voters in Texas, just as it rejected a similar challenge in 2021 to Indiana’s voting rules. It also twice declined to hear earlier versions of the Texas suit brought by the Texas Democratic Party during the COVID-19 pandemic. The challengers argued that the unequal treatment of voters is age-based discrimination prohibited by the 26th Amendment.
U.S. Supreme Court: The U.S. Supreme Court declined to take up two separate elections-related cases this week. SCOTUS rejected an appeal brought by Arizona Republicans Kari Lake and Mark Finchem, bringing finality to the duo’s legal effort challenging the use of electronic voting machines two years to the day after it began. Lake, a candidate for U.S. Senate, and Finchem, a candidate for state Senate, asked the nation’s top court to hear their case in mid-March. The court declined to consider it, making that official with an order on Monday that does not include details of the court’s decision. Legal experts had predicted the court would not exercise its discretion to add the case to its docket, citing well-established legal precedent and the court’s low acceptance rate. The court also rejected a challenge to voting rules in Texas that automatically let senior citizens − but not younger people − vote by mail. Mail-in balloting has become a partisan debate as Democrats champion it as a way to increase turnout and Republicans argue it increases the risk of voter fraud. The court declined to hear an appeal brought by three voters in Texas, just as it rejected a similar challenge in 2021 to Indiana’s voting rules. It also twice declined to hear earlier versions of the Texas suit brought by the Texas Democratic Party during the COVID-19 pandemic. The challengers argued that the unequal treatment of voters is age-based discrimination prohibited by the 26th Amendment.
 Maryland: Attorneys representing the Maryland State Board of Elections are asking District Court Judge Stephanie A. Gallagher to dismiss a lawsuit that alleges voter roll irregularities and other election law violations in the state. Two groups — Maryland Election Integrity LLC and Missouri-based United Sovereign Americans — filed suit in March against the state board for maintaining inaccurate voter registration lists and violating federal election law. Earlier this month, the groups asked Gallagher to issue an injunction against the state that could derail the May 14 primary and possibly the general election in Maryland. On April 22, an attorney representing the board responded, asking Gallagher to dismiss the lawsuit or, at a minimum, deny the request for the restraining order. “The companies’ complaint, however, fails to vest this Court with jurisdiction to entertain their accusations; and fails to factually allege a claim upon which relief could be granted. The companies allege no ‘injury in fact’ explaining how their allegations of election maladministration injured any individual member,” wrote Daniel M. Kobrin, an assistant attorney general representing the Maryland State Board of Elections. Kobrin, in his motion, writes that the two groups failed to establish standing and that their lawsuit “lacks a cognizable factual claim.” Maryland Election Integrity LLC and Missouri-based United Sovereign Americans filed suit in March alleging problems with the state’s elections.
Maryland: Attorneys representing the Maryland State Board of Elections are asking District Court Judge Stephanie A. Gallagher to dismiss a lawsuit that alleges voter roll irregularities and other election law violations in the state. Two groups — Maryland Election Integrity LLC and Missouri-based United Sovereign Americans — filed suit in March against the state board for maintaining inaccurate voter registration lists and violating federal election law. Earlier this month, the groups asked Gallagher to issue an injunction against the state that could derail the May 14 primary and possibly the general election in Maryland. On April 22, an attorney representing the board responded, asking Gallagher to dismiss the lawsuit or, at a minimum, deny the request for the restraining order. “The companies’ complaint, however, fails to vest this Court with jurisdiction to entertain their accusations; and fails to factually allege a claim upon which relief could be granted. The companies allege no ‘injury in fact’ explaining how their allegations of election maladministration injured any individual member,” wrote Daniel M. Kobrin, an assistant attorney general representing the Maryland State Board of Elections. Kobrin, in his motion, writes that the two groups failed to establish standing and that their lawsuit “lacks a cognizable factual claim.” Maryland Election Integrity LLC and Missouri-based United Sovereign Americans filed suit in March alleging problems with the state’s elections.
 Michigan: James Holkeboer, a Gaines Township poll worker will not go to trial for election fraud after a Michigan Court of Appeals threw out the case. Holkeboer was facing election fraud charges stemming from his alleged actions during last August’s primary election. Holkeboer was previously bound over for trial in 2023. Attorneys representing Holkeboer appealed the decision in May of 2023, claiming the trial court erred by interpreting MCL 168.932 “to proscribe copying election records where the statute does not use the term ‘copy’ or any of its synonyms,” Holkeboer’s attorneys wrote. Nearly a year later, the Michigan Court of Appeals agreed with that argument and dismissed the case. “The trial court erred when it denied Holkeboer’s motion to quash the bindover. The act of copying a list of voters without affecting the integrity of the document or election is not, at least at present, prohibited by MCL 168.932(c). We vacate the trial court’s order denying Holkeboer’s motion to quash and remand for an entry of an order dismissing this case,” the appeals court opinion’s conclusion reads. Kent County Prosecuting Attorney Chris Becker shared a statement after the decision to throw out the case: “I have read the opinion and I would anticipate an appeal on this issue after reviewing the reasoning. It seems a bit troubling, heading into a major presidential election, that an election worker can take information from an election computer and not be in violation of the law. I think this is an important issue that needs further review.”
Michigan: James Holkeboer, a Gaines Township poll worker will not go to trial for election fraud after a Michigan Court of Appeals threw out the case. Holkeboer was facing election fraud charges stemming from his alleged actions during last August’s primary election. Holkeboer was previously bound over for trial in 2023. Attorneys representing Holkeboer appealed the decision in May of 2023, claiming the trial court erred by interpreting MCL 168.932 “to proscribe copying election records where the statute does not use the term ‘copy’ or any of its synonyms,” Holkeboer’s attorneys wrote. Nearly a year later, the Michigan Court of Appeals agreed with that argument and dismissed the case. “The trial court erred when it denied Holkeboer’s motion to quash the bindover. The act of copying a list of voters without affecting the integrity of the document or election is not, at least at present, prohibited by MCL 168.932(c). We vacate the trial court’s order denying Holkeboer’s motion to quash and remand for an entry of an order dismissing this case,” the appeals court opinion’s conclusion reads. Kent County Prosecuting Attorney Chris Becker shared a statement after the decision to throw out the case: “I have read the opinion and I would anticipate an appeal on this issue after reviewing the reasoning. It seems a bit troubling, heading into a major presidential election, that an election worker can take information from an election computer and not be in violation of the law. I think this is an important issue that needs further review.”
 Nebraska: Secretary of State Bob Evnen and Attorney General Mike Hilgers are challenging a new law to restore felon voting rights. LB 20 gives people their voting rights immediately after finishing a sentence, including parole. There used to be a two-year waiting period. Gov. Jim Pillen says he allowed the bill to become law without his signature. But he says Evnen and Hilgers have found “significant potential constitutional” issues with the bill. Multiple groups are praising the bill, including the ACLU of Nebraska, which says it removes an arbitrary barrier to voting. Rise Nebraska says it bolsters positive social engagement.
Nebraska: Secretary of State Bob Evnen and Attorney General Mike Hilgers are challenging a new law to restore felon voting rights. LB 20 gives people their voting rights immediately after finishing a sentence, including parole. There used to be a two-year waiting period. Gov. Jim Pillen says he allowed the bill to become law without his signature. But he says Evnen and Hilgers have found “significant potential constitutional” issues with the bill. Multiple groups are praising the bill, including the ACLU of Nebraska, which says it removes an arbitrary barrier to voting. Rise Nebraska says it bolsters positive social engagement.
 New York: A New York court dismissed a challenge to the New York State Board of Elections’ approval of a touch screen voting machine, the ExpressVote XL. As of the time the lawsuit was filed, no counties had purchased the ExpressVote XL for use. Originally filed in November 2023 by Common Cause New York, the Black Institute and five New York voters, the lawsuit alleged that the state’s approval last year of the ExpressVote XL violated state law. The plaintiffs argued that the ATM-style touchscreen machine that can both mark and tabulate ballots does not allow voters to verify that their selections are correctly counted because the machine tallies the selections by producing an automated barcode. The complaint also argued that the barcode system “can (and predictably will) provide fodder for those who peddle in election voter-fraud fearmongering and conspiracy theories about ‘rigged elections’ to reduce public confidence that votes are accurately cast and counted.” The court dismissed the case after finding that those who brought the lawsuit could not show that they would be harmed by the approval of the machines.
New York: A New York court dismissed a challenge to the New York State Board of Elections’ approval of a touch screen voting machine, the ExpressVote XL. As of the time the lawsuit was filed, no counties had purchased the ExpressVote XL for use. Originally filed in November 2023 by Common Cause New York, the Black Institute and five New York voters, the lawsuit alleged that the state’s approval last year of the ExpressVote XL violated state law. The plaintiffs argued that the ATM-style touchscreen machine that can both mark and tabulate ballots does not allow voters to verify that their selections are correctly counted because the machine tallies the selections by producing an automated barcode. The complaint also argued that the barcode system “can (and predictably will) provide fodder for those who peddle in election voter-fraud fearmongering and conspiracy theories about ‘rigged elections’ to reduce public confidence that votes are accurately cast and counted.” The court dismissed the case after finding that those who brought the lawsuit could not show that they would be harmed by the approval of the machines.
 North Carolina: District Judge Loretta C. Biggs has ruled that North Carolina district attorneys cannot prosecute people on supervision for felony convictions if they mistakenly cast a ballot before regaining their right to vote. The reason, according to a ruling issued by Biggs: the underlying law was enacted to discriminate against Black North Carolinians — and continues to do so today. Plus, that law does not give prosecutors clear standards to prevent it from being enforced arbitrarily, giving district attorneys the ability to seek criminal charges based on “their personal predilections.” Biggs’ ruling is separate from the state Supreme Court’s decision because it deals with a different law. People on probation or parole for a felony will still need to complete the terms of their supervision before they can vote in North Carolina. But because of Biggs’ ruling, if those individuals unknowingly or mistakenly cast a ballot before their voting rights are restored, district attorneys cannot prosecute them. Attorneys for the State Board of Elections said the historical background of the law is “indefensible,” which Biggs called “an extraordinary and telling concession.” The state contended that a new constitution adopted in 1971 “cleansed the Challenged Statute of its discriminatory taint.” Biggs rejected that argument. That constitution expanded the scope of felony disenfranchisement to remove the right to vote of people convicted of felonies not just in North Carolina, but in other states as well. Even if the 1971 constitution did “cleanse” the underlying law, Biggs wrote, Black voters are still disproportionately impacted by the law. “Far from completely curing the law, by expanding the scope to include people convicted of felonies in other states, the constitutional amendment has presumably disenfranchised more Black people,” wrote Biggs.
North Carolina: District Judge Loretta C. Biggs has ruled that North Carolina district attorneys cannot prosecute people on supervision for felony convictions if they mistakenly cast a ballot before regaining their right to vote. The reason, according to a ruling issued by Biggs: the underlying law was enacted to discriminate against Black North Carolinians — and continues to do so today. Plus, that law does not give prosecutors clear standards to prevent it from being enforced arbitrarily, giving district attorneys the ability to seek criminal charges based on “their personal predilections.” Biggs’ ruling is separate from the state Supreme Court’s decision because it deals with a different law. People on probation or parole for a felony will still need to complete the terms of their supervision before they can vote in North Carolina. But because of Biggs’ ruling, if those individuals unknowingly or mistakenly cast a ballot before their voting rights are restored, district attorneys cannot prosecute them. Attorneys for the State Board of Elections said the historical background of the law is “indefensible,” which Biggs called “an extraordinary and telling concession.” The state contended that a new constitution adopted in 1971 “cleansed the Challenged Statute of its discriminatory taint.” Biggs rejected that argument. That constitution expanded the scope of felony disenfranchisement to remove the right to vote of people convicted of felonies not just in North Carolina, but in other states as well. Even if the 1971 constitution did “cleanse” the underlying law, Biggs wrote, Black voters are still disproportionately impacted by the law. “Far from completely curing the law, by expanding the scope to include people convicted of felonies in other states, the constitutional amendment has presumably disenfranchised more Black people,” wrote Biggs.
 Pennsylvania: Chester County County Court Judge Anthony Verwey rejected a legal motion from local Republicans that could have blocked some mail ballots from counting in this week’s Pennsylvania primary. Verwey said the Republican Committee of Chester County’s request for an injunction against the county election board would amount to “preemptively disenfranchising voters.” The lawsuit, filed April 17, contended that in 2023 the county had incorrectly interpreted the state’s mail ballot law with regards to ballots collected from a long-term care facility. The law limits ballot returns on behalf of disabled voters to one per person unless all the voters are in the same household. The law, the GOP committee argued, clearly explains that long-term care facilities should not be considered a single household, meaning residents cannot use the same staff member or volunteer to return their ballots. “The injunction proposed in this matter would disenfranchise and, therefore, harm voters who are unable to submit their ballots on their own and have already provided their mail-in ballot to a designated agent,” Verwey said in his ruling that denied the preliminary injunction while the broader lawsuit progresses.
Pennsylvania: Chester County County Court Judge Anthony Verwey rejected a legal motion from local Republicans that could have blocked some mail ballots from counting in this week’s Pennsylvania primary. Verwey said the Republican Committee of Chester County’s request for an injunction against the county election board would amount to “preemptively disenfranchising voters.” The lawsuit, filed April 17, contended that in 2023 the county had incorrectly interpreted the state’s mail ballot law with regards to ballots collected from a long-term care facility. The law limits ballot returns on behalf of disabled voters to one per person unless all the voters are in the same household. The law, the GOP committee argued, clearly explains that long-term care facilities should not be considered a single household, meaning residents cannot use the same staff member or volunteer to return their ballots. “The injunction proposed in this matter would disenfranchise and, therefore, harm voters who are unable to submit their ballots on their own and have already provided their mail-in ballot to a designated agent,” Verwey said in his ruling that denied the preliminary injunction while the broader lawsuit progresses.
 Tennessee: A federal judge ruled that Tennessee election officials cannot wrongly deny Tennesseans with past felony convictions of their right to vote by improperly rejecting eligible voters’ registration forms. In addition, the court held that the state’s registration form must properly inform potential voters with past felony convictions of their eligibility. Specifically, the court found that the state’s current practice of denying individuals the right to by rejecting voters’ registration forms when applicants indicate they have a prior felony conviction and requiring those applicants provide documentary proof of their eligibility to vote violates the National Voter Registration Act (NVRA). The court also found that Tennessee’s current voter registration form does not comply with the NVRA’s requirements for informing voters if their rights have been restored. The lawsuit alleges that Tennessee has a particularly strenuous process for restoring voting rights to those with prior felony convictions. The plaintiffs also argue that the implementation of Tennessee’s rights restoration process creates “an unequal, scattershot system across Tennessee’s ninety-five counties, causing disparate results for similarly situated individuals,” and at least one county, Rutherford County, charges a fee for the process. The plaintiffs argue that this fee constitutes a poll tax and violates the 24th Amendment. The Campaign Legal Center called this decision “a big step in the right direction” with the rest of the lawsuit’s claims set to go to trial in the coming months.
Tennessee: A federal judge ruled that Tennessee election officials cannot wrongly deny Tennesseans with past felony convictions of their right to vote by improperly rejecting eligible voters’ registration forms. In addition, the court held that the state’s registration form must properly inform potential voters with past felony convictions of their eligibility. Specifically, the court found that the state’s current practice of denying individuals the right to by rejecting voters’ registration forms when applicants indicate they have a prior felony conviction and requiring those applicants provide documentary proof of their eligibility to vote violates the National Voter Registration Act (NVRA). The court also found that Tennessee’s current voter registration form does not comply with the NVRA’s requirements for informing voters if their rights have been restored. The lawsuit alleges that Tennessee has a particularly strenuous process for restoring voting rights to those with prior felony convictions. The plaintiffs also argue that the implementation of Tennessee’s rights restoration process creates “an unequal, scattershot system across Tennessee’s ninety-five counties, causing disparate results for similarly situated individuals,” and at least one county, Rutherford County, charges a fee for the process. The plaintiffs argue that this fee constitutes a poll tax and violates the 24th Amendment. The Campaign Legal Center called this decision “a big step in the right direction” with the rest of the lawsuit’s claims set to go to trial in the coming months.
Opinions This Week
National Opinions: Threats, II | 2024 disinformation campaigns | Democracy | Election security | Noncitizen voting | Voting rights | GOP election integrity plan | Voting deserts | Election integrity
Alabama: Secretary of state, II
California: Shasta County | Voter ID
Connecticut: Absentee ballots
Indiana: Poll workers
Nevada: Threats | Protection for elections officials
Oklahoma: Ranked choice voting
Pennsylvania: Get out the vote | Voter registration | Youth vote | Vote by mail
Virginia: Ranked choice voting
Wyoming: Secretary of state | Rulemaking
Upcoming Events
The High Cost of Public Service: Threats are part of the disturbing new reality of American politics. While abuse directed at federal officeholders grabs the headlines, a new Brennan Center report reveals that intimidation aimed at state and local officials is distressingly common: 43 percent of state legislators, for example, have experienced threats within the past three years. In addition to menacing public servants and their families, these threats have serious repercussions for representative democracy. Officeholders report being less willing to work on contentious issues like reproductive rights and gun control and more reluctant to continue serving. Additionally, intimidation is often targeted at groups already underrepresented in government, such as women and people of color. Panelists Gowri Ramachandran, deputy director of the Brennan Center’s Democracy Program, Florida State Rep. Anna Eskamani, and former Nevada State Assemblymember Tom Roberts will be joined by moderator Deirdre Walsh of NPR. New York State Attorney General Letitia James, who herself has experienced threats of violence, will also deliver remarks. Where: April 30, 3pm Eastern. Where: Online
Disinformation, Elections & Democracy: Election Day 2024 will be one of the most consequential in U.S. history, and disinformation campaigns loom large in influencing millions of Americans on what’s really at stake when they head to polls this fall. Journalists across the country must be prepared with the skills to pre- and debunk conspiracy theories, misinformation, and more — well before Nov. 5. Join the National Press Club Journalism Institute for a practical look at current tactics used by disinformation specialists to disrupt the 2024 election and what journalists can do to counter them. This virtual session, will empower journalists with the tools to challenge election-specific disinformation and lies with tact and authority while respecting audiences who may be vulnerable to such campaigns.Participants will learn: The most prevalent current election disinformation tactics: What they are and how to counter them; How election administration and other public officials are addressing disinformation tactics with the public; How news organizations have found success in halting the spread of lies; and How to talk about disinformation in ways that instill trust among communities traditionally underserved by mainstream media Confirmed speakers include: Tina Barton, senior elections expert, Committee for Safe and Secure Elections; Yael Eisenstat, senior fellow at Cybersecurity for Democracy and PEN America consultant; Christine Fernando, democracy reporter, Associated Press; Sheera Frenkel, technology reporter for the New York Times; and Chad Lorenz, editor-in-chief, VoteBeat. This program is part of the Institute’s four-part training series focused on ethics in the age of disinformation. The series, produced in part with funding from the Inasmuch Foundation, is designed to provide tools and best practices to support ethical, trustworthy journalism. When: May 1. Where: Online
Focus on the Voters: It’s full steam ahead to 2024’s general election. What are lawmakers and election administrators thinking about now to prepare? Find out in this four-part series, hosted by the National Conference of State Legislatures in partnership with the U.S. Election Assistance Commission. We’ll focus on the elections workforce; counting and recounts and more post-voting work; the voters’ perspectives and voter confidence. Who are the most important people in an election? The voters. In the third installment of NCSL’s four-part webinar series on election administration, U.S. Election Assistance Commissioner Tom Hicks will address questions voters often ask and how states “get out the information” to voters. He’ll cover how states ensure the right to vote for people with disabilities and citizens living abroad (military and otherwise). When: May 10, 2pm Eastern. Where: Online.
ESRA 2024 Conference: The 8th Annual Summer Conference on Election Science, Reform, and Administration (ESRA) will be held in person from May 16-17, 2024 at the University of Southern California in Los Angeles, California. Call for Proposals The 2024 conference Call for Proposals is now open through February 16! Learn more about this year’s conference and submit your proposal here. Registration: Registration to attend the 2024 conference has not yet opened. To hear the news first when it does, please sign up to join our mailing list. When: May 16-17. Where: Los Angeles
Voter Confidence: What Can Move the Needle: It’s full steam ahead to 2024’s general election. What are lawmakers and election administrators thinking about now to prepare? Find out in this four-part series, hosted by the National Conference of State Legislatures in partnership with the U.S. Election Assistance Commission. We’ll focus on the elections workforce; counting and recounts and more post-voting work; the voters’ perspectives and voter confidence. Voter confidence is top of mind for elections stakeholders this cycle. In the final part of NCSL’s spring webinar series, U.S. Election Assistance Commissioner Christy McCormick will delve into state policies that can increase voter confidence. Perfecting processes and procedures comes first: clarifying all policies before the first vote is cast; cleaning voter lists; adopting strong chain-of-custody procedures for ballots and equipment; updating emergency plans; using pre- and post-election audits; and more. The next job is to ensure all that good technical work is transparent and communicated well to voters and the public. When: June 14, 2pm Eastern. Where: Online.
Job Postings This Week
electionlineWeekly publishes election administration job postings each week as a free service to our readers. To have your job listed in the newsletter, please send a copy of the job description, including a web link to mmoretti@electionline.org. Job postings must be received by 5pm on Wednesday in order to appear in the Thursday newsletter. Listings will run for three weeks or till the deadline listed in the posting.
Advocacy Campaign Strategist, Elections and Government Program, The Brennan Center– The Elections and Government Program is looking to hire an experienced campaign strategist. The Advocacy Campaign Strategist position reports to the DC-based Deputy Director of the Elections and Government Program. Responsibilities: Contribute to planning and execution of advocacy campaigns to achieve Elections and Government Program goals, including: Provide project management, organization, logistical solutions, and administrative support, as needed. Identify tools and methods to increase effectiveness and efficiency of team’s work. Coordinate communications between program staff and internal/external stakeholders. Engage in field advocacy, including: Participate in coalition meetings, convenings, briefings. Develop and maintain productive relationships with election officials, grassroots allies, civic partners, government staff, elected officials, and other outside stakeholders. Identify and create opportunities to advance program goals in the field, as well as to improve the program’s advocacy with learning and perspectives from the field. Conceive and execute advocacy products, such as blog posts, digital media products, public comments, FAQs, and other assets, in collaboration with communications colleagues where appropriate, with focus on broadening and increasing partner engagement with program’s work. Contribute research and writing for policy and empirical research reports that will form the basis of advocacy campaigns. Contribute to the program’s media and public education work, including strategy, talking points, and speaking engagements. Help to train new program support staff, including program associates, and serve as their first point of advice on routine matters. Application: For the complete job listing and to apply, click here.
Assistant Election Supervisor, Bartow County, Georgia– Reporting to the Elections Supervisor, this position is responsible for supervising voter registration activities as well as assisting in the coordination of federal, state, county, and municipal elections within Bartow County. Major duties: Registers voters and researches and resolves unusual and/or complicated registration issues. Maintains correct street, precinct and district information for the county; audits streets to ensure proper districting. Processes and certifies absentee ballots. Researches and determines the result of provisional ballots to make recommendations to the Board. Researches and interprets national, state and local laws as well as the rules of the State Election Board and the opinions of the Attorney General. Supervises employees by assigning registration tasks, answering questions, and coordinating schedules. Drafts and maintains written procedures for voter registration. Conducts press interviews, prepares press releases and maintains social media accounts as necessary. Troubleshoots voting issues on Election Day and during the early voting process. Compiles legally-required paperwork and supplies for Election Day and early voting. Assists in tabulating and canvassing election results. Designs and presents poll worker training. Conducts voter education and voter registration drives. Attends intergovernmental meetings with city, other county, and state agencies. Maintains office supply inventory; reorders as needed. Performs the duties of the Election Supervisor in his or her absence. Serves as Chief Deputy Registrar for the Board. Performs related duties. Salary: $51,771 to $63,107/Annually DOE/DOQ. Application: For the complete job listing and to apply, click here.
Cybersecurity Junior Analyst, Palm Beach County, Florida– The Cybersecurity Junior Analyst is responsible for monitoring the organization’s log aggregation tools and triage suspicious activity or detection alerts generated by the security controls implemented within the Supervisor of Elections Office network environment. Additionally, this position will serve as the first line of defense and response for identified security events in accordance with the Information Security Policy, and cybersecurity procedures. Candidate must be organized and personable with a great attitude, be able to work well in a team environment, calmly respond to identified security incidents, and meet deadlines under pressure. Excellent work ethic, including consistent performance, integrity, reliability, and attendance, is a must. Candidate must be detail-oriented and understand the importance of security and safety for all. Must be available 24/7 365, be able to handle simultaneous projects, be a self-starter, and remain informed on emerging threats and technologies. Application: For the complete job listing and to apply, click here.
Departmental Analyst 9-P11- Data & Programs Section, Michigan Dept. of State – This position serves as the street index and addressing administrator for the Michigan Qualified Voter File (QVF). QVF is used by all election officials, county, township, and city, statewide. This position must analyze and coordinate all activities associated with the data integrity of the street index of the QVF. Salary:$49,712 – $77,916 Annually. Deadline: April 26. Application: For the complete job listing and to apply, click here.
Deputy Director, Rhode Island Board of Elections– To assist in the planning, supervision, review of programs and administrative functions of the Elections Division as assigned; to organize, assist and direct subordinates to fulfill agency responsibilities as described in Title 17 of the Rhode Island General Laws as well as achieve agency goals and objectives, as directed by the Executive Director. SUPERVISION RECEIVED: Works under the general supervision of the Executive Director and assists in carrying out the directives and policies established by the Board. SUPERVISION EXERCISED: Assist the Executive Director supervising the permanent and seasonal staff of the Elections Division. Salary Range: $101, 756 – $116,916. Application: For the complete job listing and to apply, click here.
Deputy Director, Davie County, North Carolina – Performs clerical functions, voter registration procedures, and other election-related tasks in the daily operations of the Davie County Board of Elections, as may be assigned by the Director or Chair/members of the Board of Elections. Reports to the Elections Director and the Chair and members of the Davie County Board of Elections. Regular, predictable, full attendance is an essential function of the job. Essential Job Functions: Perform multiple functions simultaneously. Independently implement instructions delegated by the Elections Director. Perform day-to-day operations, including data entry and maintenance of voter files. Exercise considerable tact and courtesy in the course of the extensive public contact of this office and the dissemination of information to news media, political parties, candidates, and the general public. Remain politically impartial, following the statewide regulations on political activities for county board of elections employees. Other duties as assigned. Salary: Minimum hiring rate $39,000. Application: For the complete job listing and to apply, click here.
Director Board of Elections/Voter Registration, Bucks County, Pennsylvania— Are you ready to play a pivotal role in the election processes in Bucks County, the fourth largest county in the State of Pennsylvania? Are you committed to ensuring the efficient and accurate administration of elections while also maintaining the integrity of vital records of 470,992 registered voters? If so, we invite you to consider the role of Director of the Bucks County Board of Elections/Voter Registration. The Board of Elections office is at the heart of our community’s election governance, overseeing critical functions that impact every Bucks County resident. As a member of our team, you will collaborate with a dedicated group of 20 full-time and 40+ seasonal part-time employees, working under the direction of the Board of Elections/Voter Registration Director. Bucks County has an excellent benefits package including medical, vision, dental, and prescription as well as an employer-matched retirement program. Bucks County is a wonderful community to live, work, and play and is uniquely located along the I-95 Corridor. Directs operation of the offices of Board of Elections, Voter Registration, and Voting Machines. This includes planning and conducting elections, voter registration management, and ensuring compliance with election laws and regulations. The Director is responsible for training election staff, overseeing technological security measures to safeguard voting integrity as well as creating an annual budget. Communicates election information to the Board of Elections, County administration, and the public. Addresses any issues or concerns that may arise during the election process. Application: For the complete job listing and to apply, click here.
Elections and Democracy Fellow, Center for Democracy & Technology– The Elections and Democracy Fellow will contribute to the organization’s work across these issues, particularly focusing on threats to the online information environment. The position requires a combination of research and advocacy skills to respond to emerging issues. Responsibilities: Conducting research on key issues impacting the information environment around elections, in order to raise awareness about vulnerabilities, highlight best practices, and develop/disseminate recommendations for generative AI companies, social media platforms, election officials, political campaigns, and other actors. Authoring policy papers, reports, blog posts, and similar materials. Engaging directly with technology companies to develop best practices and policy recommendations. Serving as a resource to federal and state governments and political campaigns as they enact new policies and practices on the use of generative AI in political advertising and campaigning. Coordinating advocacy efforts with other civil society organizations that have a shared interest in elections and democracy and the online information environment. Assisting with tracking and analyzing federal and state proposals to regulate generative AI and other elections-related legislation. Convening and engaging with technical experts, election vendors, election officials, voting and democracy advocates, academics and other stakeholders working on issues within the project’s scope. Supporting research, preparation, and operationalization of trainings for election officials and other stakeholders. Collaborating with CDT’s teams focused on free expression/online platform governance; technology & disability rights; AI governance, and consumer privacy; as well as CDT’s Research team and non-resident Research Fellows. Salary $65K-$105K. Application: For the complete job listing and to apply, click here.
Elections and Registration Specialist, Virginia Department of Elections– The Elections and Registration Specialist ensures compliance with state and federal laws regarding the administration of elections. Collaborate with multiple internal and external partners to ensure the agency fosters an integrated approach to election administration policy and procedures. Provide appropriate guidance and support to Virginia’s election officials and Department of Elections (ELECT) staff via research, process supervision and liaison activities. The Department of Elections promotes and supports accurate, fair, open and secure elections for the citizens of the Commonwealth. Elect ensures the proper administration of election laws, campaign finance disclosure compliance, and voter registration processes in the state by promulgating rules, regulations, issuing instructions, and providing information to local Electoral Boards and general registrars. The Department of Elections envisions a highly modern, efficient and professional electoral process that is trustworthy and accountable at all levels and engages Virginia’s diverse citizenry in the most fundamental right in a democratic society: the right to vote. Salary: Hiring range up to $65K. Deadline: April 25. Application: For the complete job listing and to apply, click here.
Elections Technology Specialist, McLennan County, Texas– Under supervision of the Elections Administrator, the Elections Technology Specialist performs complex and technical duties related to activities in overseeing the County’s voting equipment by creating each election’s ballot using ballot origination software, programing and testing the County’s voting equipment with each elections ballot, processing and scanning returned mail-in ballots with the Ballot Board, and maintaining the County’s voting equipment after each election. Salary: $19.92 – $31.72 Hourly. Deadline: June 20. Application: For the complete job listing and to apply, click here.
Executive Director– The American Council of Election Technology (ACET), a national, nonpartisan trade association of the leading providers of election technology solutions, is currently conducting a search for a dynamic, well-connected, hard-working election professional who loves this field and the people in it, to serve as ACET’s Executive Director to work with the group under contract throughout the remainder of calendar year 2024. (For 2025 and beyond, this position will be contracted annually from January through December.) Please see our detailed LinkedIn post for more information. If you are interested in discussing this exciting opportunity, please inbox Michelle Shafer on LinkedIn (Michelle is currently consulting with ACET to help coordinate this search.) or send a resume and cover letter to ACET at info@techforelections.vote. The American Council of Election Technology (ACET) is a national, nonpartisan trade association of the leading providers of election technology solutions. Thousands of jurisdictions across the United States rely on our members’ products and services to advance democracy. ACET members provide voters with the means to cast their ballots with confidence that their votes will be accurately recorded and protected. Their technologies and services help state and local officials print ballots, check-in voters, tabulate votes, and report and audit election results. Current ACET Member Companies are: Election Systems & Software, Hart InterCivic, MicroVote, Runbeck Election Services, Smartmatic, Unisyn Voting Solutions, VOTEC Corporation. Application: For the complete job listing and to apply, click here.
Field Operations Coordinator, Hays County, Texas– Reporting directly to Election Network Engineer, responsible for overseeing the inventory, distribution, maintenance, warehouse storage, and logistics of all equipment, voting ballots, and department assets for Hays County Elections Department. Responsible for identifying and reserving polling sites including overseeing the coordination of all polling site compliance and usage. Ensures polling locations follow the Texas Election Code for early voting and election day. Oversees the day-to-day tasks of the election technicians’ program. Salary: $46,378 – $50,678. Annually Application: For the complete job listing and to apply, click here.
GIS Specialist, Palm Beach County, Florida– The GIS Specialist position requires technical level aptitude involving geospatial data management, analysis, and cartography using Geographic Information Systems (GIS). The position is responsible for the successful creation, maintenance and update of complex database information and support of GIS projects and initiatives. Perform GIS data development activities, including developing and updating GIS databases from hard copy maps, site plans, existing electronic data sets, and GPS (Global Positioning System). Identifies and accounts for differences in map projections and overlay of information from different sources. Duties include establishing, implementing and maintaining standards and procedures for database management, development and documentation. Develops map layouts, web accessible maps and logistics maps. Maintain data synchronization between GIS and Voter Registration System. Must have proficient computer skills, knowledge of relational databases, ability to handle simultaneous multiple projects and be a self-starter. Application: For the complete job listing and to apply, click here.
Operations Associate, NASED– A part-time (approximately 20 hours per week), fully remote, Operations Associate for a small nonpartisan, nonprofit membership association. Reporting to the Executive Director, this new role will support all the organization’s operational needs. The responsibilities of this position will include, but are not limited to, the following: Help update and maintain website content; Help maintain NASED’s social media presence, including developing content and creating basic graphics; Work with NASED’s controller on monthly financial reports and with the auditor and accountant on annual reports and filings; Monitor and assist with responses to inquiries sent to NASED’s shared inboxes; Maintain organization distribution lists; Assist with scheduling Board and Committee meetings; Assist with conference planning, including developing the conference website via the conference management platform, creating and proofing materials, planning activities, and budgeting; Support the execution of two national conferences per year; Create and send annual invoices to organization members and Corporate Affiliate members; and Other duties and special projects as assigned. This position is part-time and fully remote, but the candidate must live in the United States. Travel to support NASED’s Winter and Summer conferences is required (approximately 10 days per year). This position reports to NASED’s Executive Director. This role does not supervise any staff. Application: For the complete job listing and to apply, click here.
Physical Security Specialist, Palm Beach County, Florida– This position is responsible for administration of the physical security programs in a manner consistent with Supervisor of Elections Office policies, procedures, quality standards, and applicable local, state, and federal regulations. These programs include conducting facility security risk assessments, assisting with access control, monitoring alarms and CCTV systems, and providing security related training. Must be organized and personable with a great attitude, be able to work well in a team environment, and meet deadlines under pressure. Excellent work ethic, including consistent performance, integrity, reliability, and attendance, is a must. Candidate must be detail-oriented and understand the importance of security and safety for all. Must be available 24/7 365, be able to handle simultaneous projects, and be a self-starter. Application: For the complete job listing and to apply, click here.
Registrar of Voters, San Bernardino County, California– The county of San Bernardino is seeking a visionary new registrar of voters to oversee the critical activities of the Registrar’s office with a large scope of oversight including 50+ members and an annual budget of $20M+. The Registrar of Voters will foster an environment that promotes civic participation and ensures transparent and fair elections. They will design and implement voter education programs tailored to the needs of County residents. This position requires a deep understanding of the County’s diverse demographics, its unique challenges, and the ability to implement strategies that promote voter engagement, education, and participation. The Registrar will oversee voter registration efforts, ensuring that registration processes are accessible, efficient, and in compliance with state and federal regulations. They will work closely with local community organizations, schools, and governmental entities to create outreach initiatives and workshops to increase countywide engagement. Engaging with the community is at the heart of this role. Building and maintaining strong relationships with various stakeholders, including community leaders, advocacy groups, and residents, is paramount. Organizing town hall meetings, forums, and public discussions will be essential to address concerns, gather feedback, and disseminate essential information related to voting procedures, ballot measures, and electoral reforms. By actively listening to the community’s needs and concerns, they will play a pivotal role in shaping policies and initiatives that resonate with the diverse population of San Bernardino County. This position offers a unique opportunity for development and growth within the realm of civic engagement and electoral processes. As the landscape of voting rights, technologies, and methodologies continues to evolve, staying abreast of emerging trends, best practices, and legislative changes is essential. Participating in training programs, conferences, and workshops will enhance the knowledge base, skill set, and capacity to navigate the complexities associated with administering elections in the County. Salary: $153,504-$218,004. Application: For the complete job listing and to apply, click here.
Senior Counsel, Voting Rights Program, The Brennan Center– The Brennan Center’s Voting Rights Program seeks a talented attorney to join our team working to build a robust, participatory, and inclusive democracy. Reporting to the Director of the Voting Rights Program, the attorney’s focus will be to combat voter suppression and advance pro-voter reforms at the state and federal levels. Our Voting Rights Program advocates for free, fair, and accessible elections, with special focus on the ways systemic barriers impede electoral participation by communities of color. The past ten years have seen a renewed brazen and widespread assault on the right to vote. Elected officials at the highest levels have deployed disinformation and misinformation to scapegoat communities trying to assert their rightful place in the electorate. And the Capitol attack made plain that some are even prepared to reject the use of elections as the arena to contest political differences. We meet these challenges, and others, head on. We do so with partners ranging from community-based organizations to election administrators to pro bono counsel. The Brennan Center’s methods include legal and empirical research and writing, litigation, legislative and policy advocacy, media and communications, and public education. Salary: $145,100 – $185,800. Application: For the complete job listing and to apply, click here.
Senior Director, Election Law Program, William & Mary–The Election Law Program (ELP), a joint initiative of the William and Mary Law School and the National Center for State Courts, has a mission to provide resources for judges deciding election disputes. This vacancy is for an experienced attorney to serve in the role of Senior Director of the Election Law Program. The Senior Director will be an attorney with experience in election law. Reporting to the ELP Co-Directors, the portfolio of responsibilities will include, but not be limited to: Developing resources for judges deciding election cases; Supporting projects that enhance understanding of federal and state election laws and the role of courts in resolving election disputes; Sharing research findings and legal resources through a variety of mechanisms such as publications and educational programs (e.g., webinars, presentations, and conferences); Overseeing ELP project implementation; Identifying and capturing trends in election litigation; Engaging in collaborative projects with trusted partners; Supervising student research; and Participating in fundraising efforts to support existing and future ELP initiatives as required. NOTE: If interested, an opportunity for appointment as an adjunct professor to teach a relevant course within the field of election law is available. Salary: $110,000 to $125,000, commensurate with experience. Application: For the complete job listing and to apply, click here.
Voter Services Manager, Arapahoe County, Colorado– The Voter Service Manager position has direct responsibility and supervision of the entire Voter Service Team. This position will assist with complex administrative and supervisory work in directing daily activities. The Voter Service Manager supports the Elections Deputy Director, Chief Deputy Director and the Clerk and Recorder with issues concerning all operations of Elections. The following statements are illustrative of the essential function of the job. Salary: $73,441.94 – $117,316.94 Annually. Deadline: April 29. Application: For the complete job listing and to apply, click here.
Marketplace
electionline provides no guarantees as to the quality of the items being sold and the accuracy of the information provided about the sale items in the Marketplace. Ads are provided directly by sellers and are not verified by electionline. If you have an ad for Marketplace, please email it to: mmoretti@electionline.org